Phishing Attempts Through Steam: When Enemies Turn Into 'Friends'
Last week, a friend of mine notified our group that most of his social media accounts had been broken into. Login attempts were unsuccessful on often-used apps. It appeared as if the malicious actor used a cracked password to laterally gain access to his other accounts. Regardless, a major headache in this day and age, especially with all the personal information available online.
Following a brisk Thursday afternoon, I sat down at my desk to continue my studies and learning modules. Upon logging into my desktop, Steam immediately greeted me with a Direct Message (DM) from my friend. Immediately, of course, alarm bells started ‘sounding’ in my head. “If they were able to message me then his entire Steam account and its contents are breached as well.” Contacting him back confirmed my suspicions; someone gained access to his account and changed all the passwords, effectively locking him out.
Message Content
The message content itself was extremely suspicious. The message appears in the image below and reads “STEAM GIVES THE GIFT - https://[malicious-url]”.
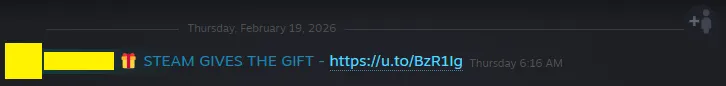
We can see a shortened URL was used to redirect the victim to the malicious site. It may seem inconspicuous, however that is the intention; if the URL read definitely-not-malicious.to/ we would of course be immediately worried. However, there is no indication within the URL provided to show malicious intent.
Performing a URL Scan
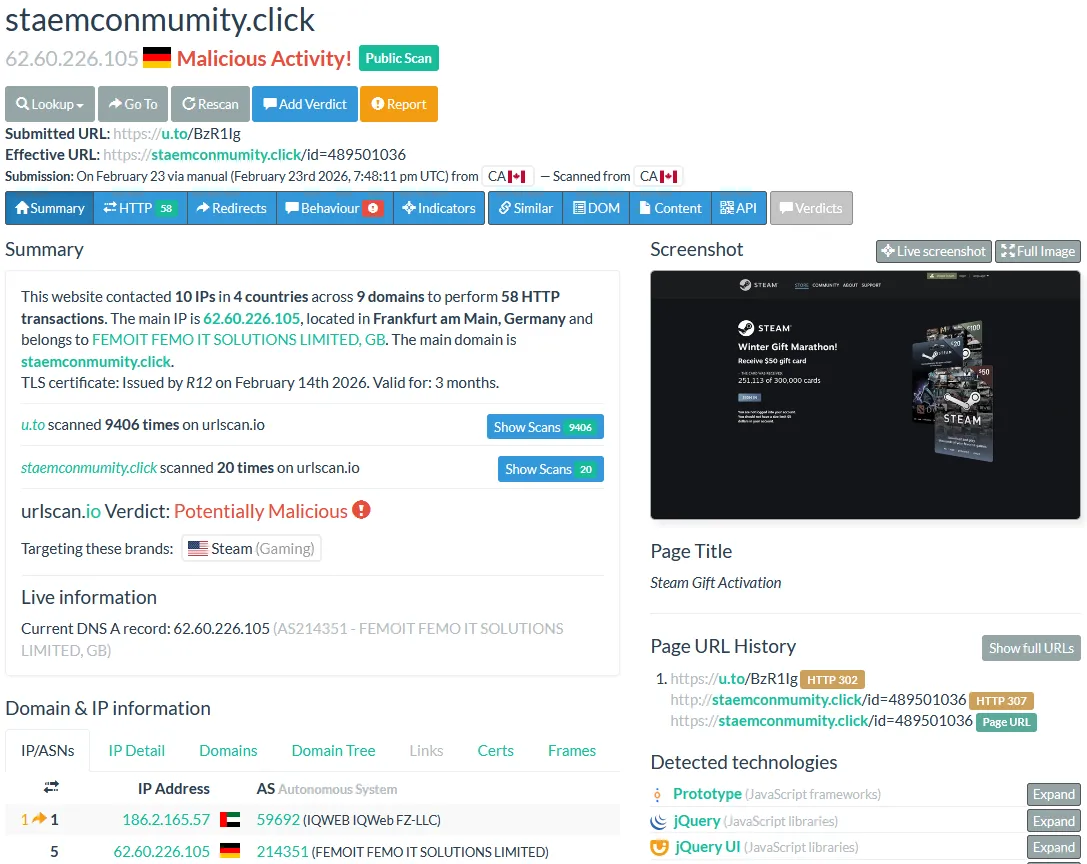
Using the OSINT tool urlscan.io I performed multiple scans on the shortened URL. And the results were quite shocking to me. You can view the results in the image below.
Scan Results
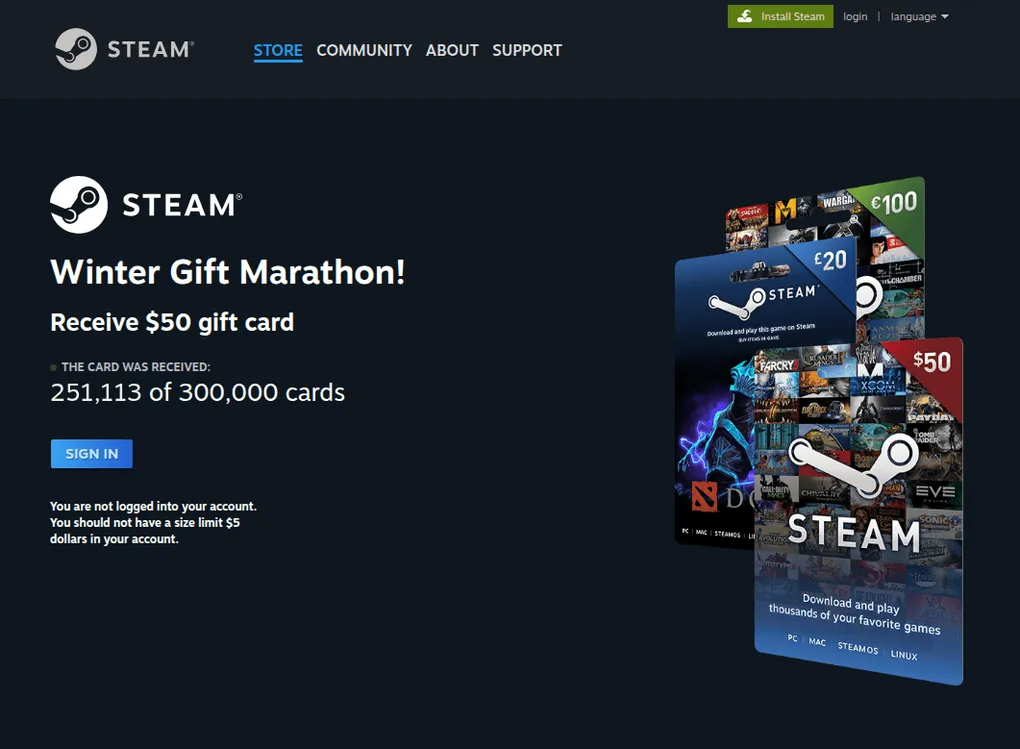
My suspicions were right on the nose- the shortened URL redirects the unsuspecting victim to a fake Steam-appearing page where they can enter to win $50 Steam gift cards. In fact, the domain name was hilariously a misspelling of the expected Steam Community domain: staemconmumity(dot)click. I had a chuckle to myself. I can understand why they wanted to hide that domain name.
Parsing through the scan’s results, here is some information I extrapolated about the malicious link.
- The main website IP belongs to FEMO IT SOLUTIONS LIMITED hosted in Frankfurt am Main, Germany, a recently established network from August 2024.
- Classified by major threat intelligence organizations as a Threat Activity Enabler (TAE).
- The other ASN anomaly refers to the UAE IP. The infrastructure, while under the guise of a shell company in the Middle East, is actually operated by known malicious actors DDoS-Guard, a Russian-operated ISP and DDoS mitigation service.
- Notorious for being a bulletproof host: a service provider that deliberately turns a blind eye to the content on their services and ignore reports, DMCA notices, and law enforcement takedown requests.
- The target domain is masking its true origin through standard Content Delivery Networks (CDN) but the backend traffic clearly directs us to the malicious infrastructure.
I decided to investigate further to see if I could identify any Indicators of Compromise (IoC). Viewing 58 total HTTP transactions, one script appears to stand out as an IoC. It is a JavaScript .js filetype, meaning it can run any dedicated scripts. The name of the file is in hexadecimal as an attempt to obfuscate the real intention. In addition, this file was 253KB in size. After writing my own code and better understanding the size files can reach, this appears to be a larger script. This is most likely where the malicious code lives to potentially capture keystrokes, intercept Steam Guard 2FA codes, and format the stolen credentials.
Conclusion & Key Takeaways
This investigation served as a stark reminder of how sophisticated everyday phishing campaigns have become. The threat actors didn’t just spin up a cheap, easily traceable server; they deliberately routed their traffic through bulletproof hosts and utilized heavy JavaScript payloads specifically designed to harvest credentials and potentially intercept 2FA tokens on the fly.
Here are the major takeaways from dissecting this attack:
- The Danger of Password Reuse: The entire chain of events started because a single compromised password allowed lateral movement across my friend’s digital footprint. Using a password manager to generate and store unique, complex credentials for every service is an absolute necessity to contain potential breaches.
- Verify the Destination: Shortened URLs in direct messages—even from trusted friends—should always be treated as hostile until proven otherwise. The
staemconmumitytyposquat is a classic, highly effective trick that relies entirely on the victim rushing to claim a “prize.” - The Power of OSINT: Relying on tools like
urlscan.ioallows for deep, comprehensive analysis of malicious infrastructure without ever exposing a local machine to the payload. It cleanly strips away the CDN camouflage to reveal the true threat actors hosting the site. - The Need for Isolated Analysis: While web-based OSINT tools provided the network blueprint, having a dedicated, isolated sandbox environment is the logical next step for safely downloading and reverse-engineering that 253KB JavaScript file to map out its exact execution flow and behavior.
Unfortunately, despite efforts to work with support, my friend was unable to recover his account. The permanent loss of his library and the ongoing headache of securing his remaining digital footprint is a harsh reminder of exactly how damaging these attacks are.
Stay vigilant, and always verify before you click.
AD.